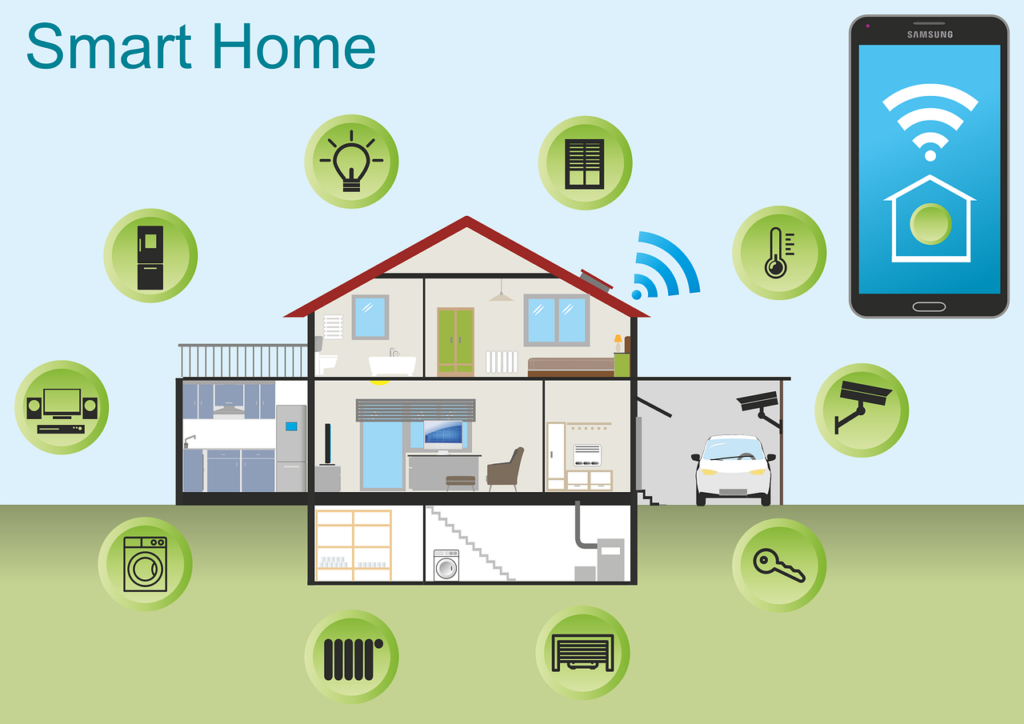
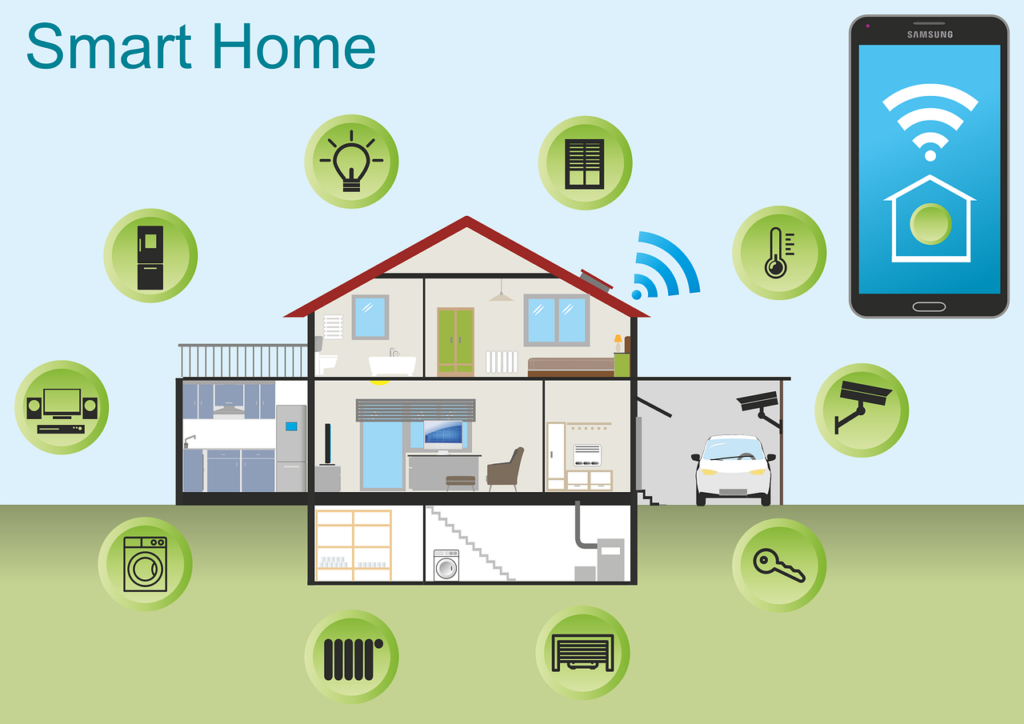
10 Most Common Smart Home Issues (and How to Fix Them)
Back when you were a kid, living in a “smart home” probably sounded futuristic. Something out of Back to the Future II or The Jetsons. Well, we don’t yet have flying cars, but we do have video telephones as well as smart refrigerators
Eye-opening Insights from the 2023 Annual Cybersecurity Attitudes and Behaviors Report

We are living in an era dominated by digital connectivity. You can’t overstate the importance of cybersecurity. As technology advances, so do the threats that lurk in the online world.Often, it’s our own actions that leave us most at risk of a cyberattack
Be Careful When Scanning QR Codes – There’s a New Scam Going Around!

QR codes are everywhere these days. You can find them on restaurant menus, flyers, and posters. They’re used both offline and online. QR codes are convenient and easy to use. You just scan them with your smartphone camera. You’re then directed to a
Smart Tactics to Reduce Cloud Waste at Your Business

Cloud computing has revolutionized the way businesses operate. It offers scalability, flexibility, and cost-efficiency. But cloud services also come with a downside: cloud waste.Cloud waste is the unnecessary spending of resources and money on cloud services. These services are often not fully utilized
What Is Microsoft Security Copilot? Should You Use It?

It can be challenging to keep up with the ever-evolving cyber threat landscape. Companies need to process large amounts of data. As well as respond to incidents quickly and effectively. Managing an organization’s security posture is complex.That’s where Microsoft Security Copilot comes in.
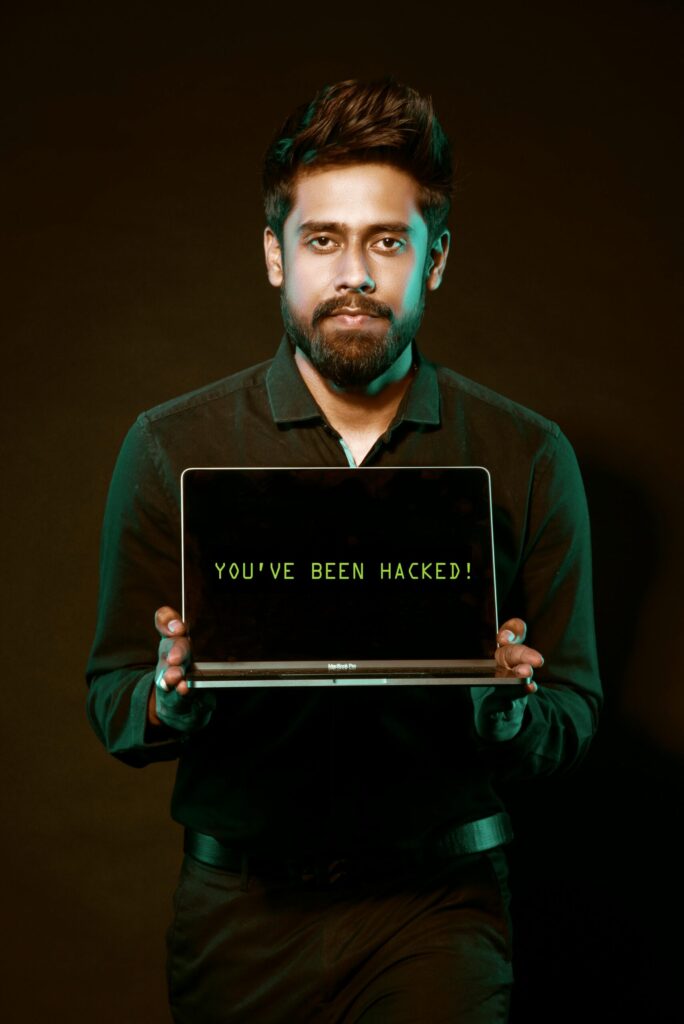
9 Signs That Your Smart Home Device Has Been Hacked
Smart home devices are becoming more popular and convenient. But they also pose some serious security risks. Hackers can target these devices to access your personal information. As well as spy on your activities or cause damage to your home.Often the dangers of
5 Cybersecurity Predictions for 2024 You Should Plan For

Cybersecurity is a constantly evolving field. There are new threats, technologies, and opportunities emerging every year. As we enter 2024, organizations need to be aware of current and future cyber threats. Businesses of all sizes and sectors should plan accordingly.Staying ahead of the
Online Security: Addressing the Dangers of Browser Extensions

Browser extensions have become as common as mobile apps. People tend to download many and use few. There are over 176,000 browser extensions available on Google Chrome alone. These extensions offer users extra functionalities and customization options.While browser extensions enhance the browsing experience,
Coolest Smart Gadgets at Europe’s Biggest Tech Trade Show (IFA)

Every year, tech enthusiasts eagerly anticipate Europe's most prominent technology trade show. It’s the Internationale Funkausstellung Berlin, or simply IFA.This is a showcase of the latest and greatest innovations in consumer electronics. The show includes everything from cutting-edge smartphones to futuristic smart home
Choose Wisely: What Smart Home Tech Should You Adopt and Avoid?

In the age of smart living, our homes are becoming increasingly intelligent. They’re designed to cater to our every need. Smart gadgets are transforming how we turn on the lights, home security, and more. They even help us feed our pets from afar.But
9 Smart Ways for Small Businesses to Incorporate Generative AI
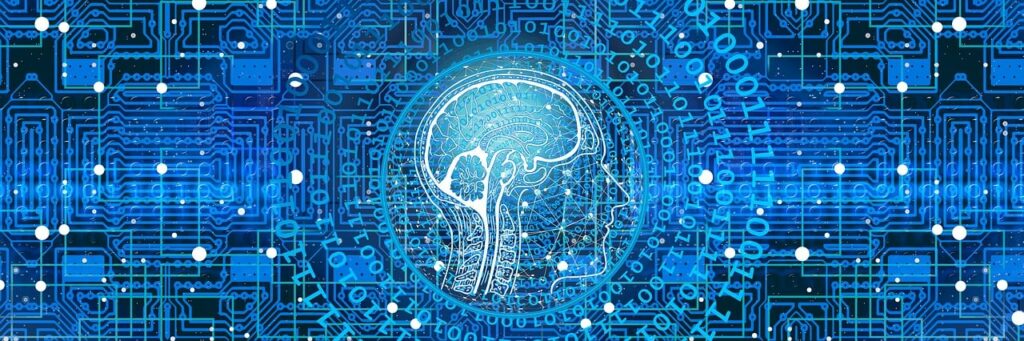
There is no escaping the relentless march of AI. Software companies are rapidly incorporating it into many business tools. This includes tools like Microsoft 365, Salesforce, and others.Many people are still concerned about where AI will go. But there is no denying that